🚨 Introduction How a WinRAR Bug Could Let Hackers Take Control. WinRAR is one of the most popular tools for compressing and extracting files, used by both individuals and organizations. A serious secu...
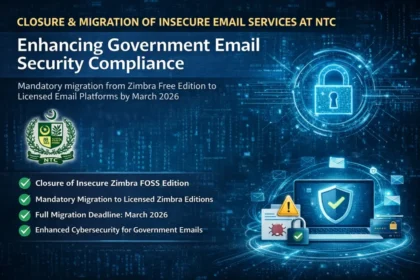
Introduction: Why Secure Government Email Systems Matter Email remains the primary communication backbone for government departments, enabling daily coordination, policy execution, and information exc...
Why the Android Zero-Day Exploit Is a Serious Concern Android Zero-Day Exploit Alert 2025: Critical Security Threat Affecting Millions of Devices. In December 2025, Google confirmed the discovery of m...
Cybersecurity & Personal Digital Safety: Stay Safe Online : As our lives move increasingly online, the threat of cyberattacks, data breaches, and scams grows. This creates a constant and urgent ne...
We’ve all been there. You’re logging into your favorite shopping site, your email, or your bank, and a little box pops up: “Save password?” Your finger hovers over the mouse. It’s so tempt...
Protecting Your Mobile Device from Cyber Attacks: A Complete Guide. In today’s hyper-connected world, mobile devices have become more than just communication tools. They serve as personal assistants, ...
This article is about New Cybersecurity Warning: Ransomware Actors Tied to Lock Bit Mora_001, a ransomware group linked to LockBit, is the subject of an upcoming discussion. The group has been activel...
Here are the Top 5 IT solutions for corporations Artificial Intelligence (AI) and Machine Learning (ML): Business operations and service delivery are changing as a result of AI and ML. Content and cod...
The importance of Information Security in today’s digital age, information security is more crucial than ever. With the rise of cyber threats and data breaches, protecting sensitive information ...
Understanding New Technologies In today’s rapidly evolving tech landscape, staying informed is crucial. The integration of artificial intelligence (AI), machine learning, and the Internet of Thi...